Merge branch 'main' of gitlab.com:domaindrivenarchitecture/c4k-jitsi
This commit is contained in:
commit
b627e3d5c1
23 changed files with 180 additions and 517 deletions
.gitlab-ci.ymlREADME.mdcreate_admin.shtest.yamlvalid-auth.ednvalid-config.edn
doc
package.jsonproject.cljshadow-cljs.ednsrc
main
clj/dda/c4k_jitsi
cljc/dda/c4k_jitsi
cljs/dda/c4k_jitsi
resources/jitsi
test
|
|
@ -48,7 +48,7 @@ test-schema:
|
|||
stage: build_and_test
|
||||
script:
|
||||
- lein uberjar
|
||||
- java -jar target/uberjar/c4k-jitsi-standalone.jar valid-config.edn valid-auth.edn | kubeconform --kubernetes-version 1.19.0 --strict --skip Certificate -
|
||||
- java -jar target/uberjar/c4k-jitsi-standalone.jar src/test/resources/jitsi-test/valid-config.yaml src/test/resources/jitsi-test/valid-auth.yaml | kubeconform --kubernetes-version 1.19.0 --strict --skip Certificate -
|
||||
artifacts:
|
||||
paths:
|
||||
- target/uberjar
|
||||
|
|
|
|||
|
|
@ -25,8 +25,8 @@ Your input will stay in your browser. No server interaction is required.
|
|||
|
||||
You will also be able to try out on cli:
|
||||
```
|
||||
target/graalvm/c4k-jitsi src/test/resources/valid-config.edn src/test/resources/valid-auth.edn | kubeval -
|
||||
target/graalvm/c4k-jitsi src/test/resources/valid-config.edn src/test/resources/valid-auth.edn | kubectl apply -f -
|
||||
target/graalvm/c4k-jitsi src/test/resources/jitsi-test/valid-config.yaml src/test/resources/jitsi-test/valid-auth.yaml | kubeval -
|
||||
target/graalvm/c4k-jitsi src/test/resources/jitsi-test/valid-config.yaml src/test/resources/jitsi-test/valid-auth.yaml | kubectl apply -f -
|
||||
```
|
||||
|
||||
## Documentation
|
||||
|
|
|
|||
|
|
@ -1,9 +0,0 @@
|
|||
#!/bin/bash
|
||||
|
||||
if [ $# != 4 ]
|
||||
then
|
||||
echo "expected 4 arguments (webserver-pod-name, username, email, password)"
|
||||
exit -1
|
||||
fi
|
||||
|
||||
kubectl exec $1 -- python3 manage.py shell -c "from django.contrib.auth import get_user_model; User = get_user_model(); User.objects.create_superuser('$2', '$3', '$4')"
|
||||
|
|
@ -45,7 +45,7 @@ output "ipv4" {
|
|||
|
||||
## k8s minicluster
|
||||
|
||||
For k8s installation we use our [dda-k8s-crate](https://github.com/DomainDrivenArchitecture/dda-k8s-crate) with the following configuation:
|
||||
For k8s installation we use our [provs](https://repo.prod.meissa.de/meissa/provs) with the following configuation:
|
||||
|
||||
|
||||
```
|
||||
|
|
@ -69,5 +69,5 @@ with the following config.edn:
|
|||
```
|
||||
{:fqdn "the-fqdn-from aws_route53_record.v4_neu"
|
||||
:postgres-data-volume-path "/var/postgres" ;; Volume was configured at dda-k8s-crate, results in a PersistentVolume definition.
|
||||
:issuer :prod }
|
||||
:issuer "prod" }
|
||||
```
|
||||
|
|
|
|||
BIN
doc/tryItOut.png
BIN
doc/tryItOut.png
Binary file not shown.
|
Before 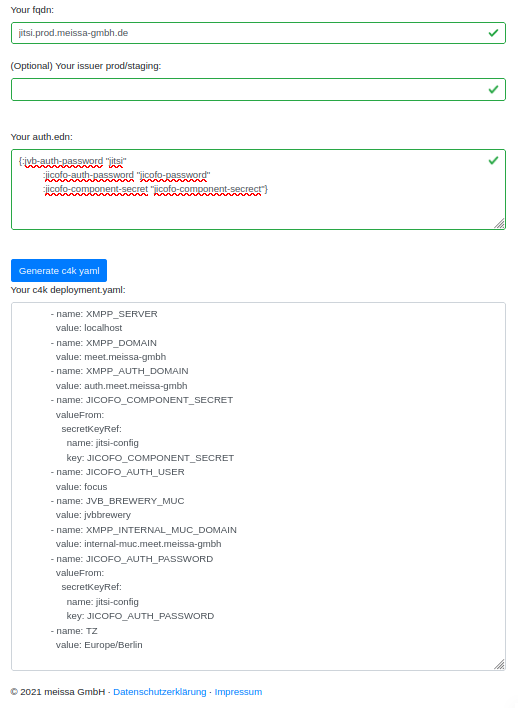
(image error) Size: 48 KiB After 
(image error) Size: 83 KiB 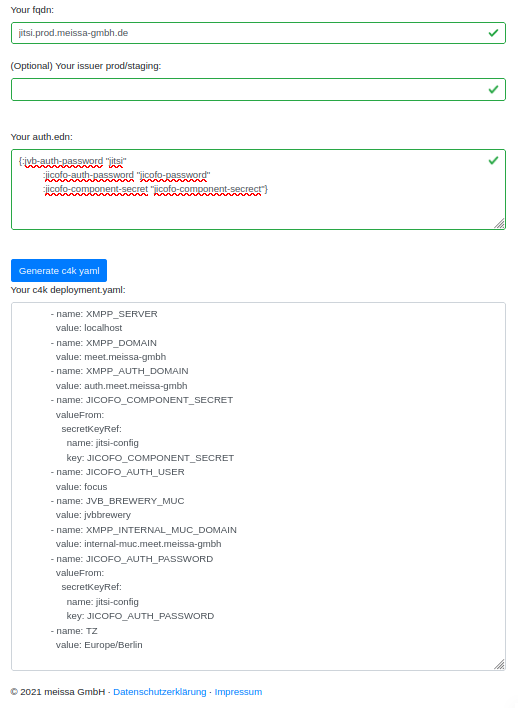

|
|
|
@ -2,7 +2,7 @@
|
|||
"name": "c4k-jitsi",
|
||||
"description": "Generate c4k yaml for a jitsi deployment.",
|
||||
"author": "meissa GmbH",
|
||||
"version": "1.2.2-SNAPSHOT",
|
||||
"version": "1.3.2",
|
||||
"homepage": "https://gitlab.com/domaindrivenarchitecture/c4k-jitsi#readme",
|
||||
"repository": "https://www.npmjs.com/package/c4k-jitsi",
|
||||
"license": "APACHE2",
|
||||
|
|
|
|||
12
project.clj
12
project.clj
|
|
@ -1,11 +1,11 @@
|
|||
(defproject org.domaindrivenarchitecture/c4k-jitsi "1.2.2-SNAPSHOT"
|
||||
(defproject org.domaindrivenarchitecture/c4k-jitsi "1.3.3-SNAPSHOT"
|
||||
:description "jitsi c4k-installation package"
|
||||
:url "https://domaindrivenarchitecture.org"
|
||||
:license {:name "Apache License, Version 2.0"
|
||||
:url "https://www.apache.org/licenses/LICENSE-2.0.html"}
|
||||
:dependencies [[org.clojure/clojure "1.10.3"]
|
||||
:dependencies [[org.clojure/clojure "1.11.1"]
|
||||
[org.clojure/tools.reader "1.3.6"]
|
||||
[org.domaindrivenarchitecture/c4k-common-clj "2.1.0"]
|
||||
[org.domaindrivenarchitecture/c4k-common-clj "5.0.1"]
|
||||
[hickory "0.7.1"]]
|
||||
:target-path "target/%s/"
|
||||
:source-paths ["src/main/cljc"
|
||||
|
|
@ -22,10 +22,10 @@
|
|||
:uberjar {:aot :all
|
||||
:main dda.c4k-jitsi.uberjar
|
||||
:uberjar-name "c4k-jitsi-standalone.jar"
|
||||
:dependencies [[org.clojure/tools.cli "1.0.206"]
|
||||
[ch.qos.logback/logback-classic "1.3.0-alpha4"
|
||||
:dependencies [[org.clojure/tools.cli "1.0.214"]
|
||||
[ch.qos.logback/logback-classic "1.4.5"
|
||||
:exclusions [com.sun.mail/javax.mail]]
|
||||
[org.slf4j/jcl-over-slf4j "2.0.0-alpha1"]]}}
|
||||
[org.slf4j/jcl-over-slf4j "2.0.6"]]}}
|
||||
:release-tasks [["test"]
|
||||
["vcs" "assert-committed"]
|
||||
["change" "version" "leiningen.release/bump-version" "release"]
|
||||
|
|
|
|||
|
|
@ -4,7 +4,7 @@
|
|||
"src/test/cljc"
|
||||
"src/test/cljs"
|
||||
"src/test/resources"]
|
||||
:dependencies [[org.domaindrivenarchitecture/c4k-common-cljs "1.0.0"]
|
||||
:dependencies [[org.domaindrivenarchitecture/c4k-common-cljs "5.0.1"]
|
||||
[hickory "0.7.1"]]
|
||||
:builds {:frontend {:target :browser
|
||||
:modules {:main {:init-fn dda.c4k-jitsi.browser/init}}
|
||||
|
|
|
|||
|
|
@ -1,56 +1,14 @@
|
|||
(ns dda.c4k-jitsi.uberjar
|
||||
(:gen-class)
|
||||
(:require
|
||||
[clojure.spec.alpha :as s]
|
||||
[clojure.string :as cs]
|
||||
[clojure.tools.reader.edn :as edn]
|
||||
[expound.alpha :as expound]
|
||||
[dda.c4k-common.uberjar :as uberjar]
|
||||
[dda.c4k-jitsi.core :as core]))
|
||||
|
||||
(def usage
|
||||
"usage:
|
||||
|
||||
c4k-jitsi {your configuraton file} {your authorization file}")
|
||||
|
||||
(s/def ::options (s/* #{"-h"}))
|
||||
(s/def ::filename (s/and string?
|
||||
#(not (cs/starts-with? % "-"))))
|
||||
(s/def ::cmd-args (s/cat :options ::options
|
||||
:args (s/?
|
||||
(s/cat :config ::filename
|
||||
:auth ::filename))))
|
||||
|
||||
(defn expound-config
|
||||
[config]
|
||||
(expound/expound ::core/config config))
|
||||
|
||||
(defn invalid-args-msg
|
||||
[spec args]
|
||||
(s/explain spec args)
|
||||
(println (str "Bad commandline arguments\n" usage)))
|
||||
|
||||
(defn -main [& cmd-args]
|
||||
(let [parsed-args-cmd (s/conform ::cmd-args cmd-args)]
|
||||
(if (= ::s/invalid parsed-args-cmd)
|
||||
(invalid-args-msg ::cmd-args cmd-args)
|
||||
(let [{:keys [options args]} parsed-args-cmd
|
||||
{:keys [config auth]} args]
|
||||
(cond
|
||||
(some #(= "-h" %) options)
|
||||
(println usage)
|
||||
:default
|
||||
(let [config-str (slurp config)
|
||||
auth-str (slurp auth)
|
||||
config-edn (edn/read-string config-str)
|
||||
auth-edn (edn/read-string auth-str)
|
||||
config-valid? (s/valid? core/config? config-edn)
|
||||
auth-valid? (s/valid? core/auth? auth-edn)]
|
||||
(if (and config-valid? auth-valid?)
|
||||
(println (core/generate config-edn auth-edn))
|
||||
(do
|
||||
(when (not config-valid?)
|
||||
(println
|
||||
(expound/expound-str core/config? config-edn {:print-specs? false})))
|
||||
(when (not auth-valid?)
|
||||
(println
|
||||
(expound/expound-str core/auth? auth-edn {:print-specs? false})))))))))))
|
||||
(uberjar/main-common
|
||||
"c4k-jitsi"
|
||||
core/config?
|
||||
core/auth?
|
||||
core/config-defaults
|
||||
core/k8s-objects
|
||||
cmd-args))
|
||||
|
|
|
|||
|
|
@ -1,35 +1,41 @@
|
|||
(ns dda.c4k-jitsi.core
|
||||
(:require
|
||||
[clojure.string :as cs]
|
||||
[clojure.spec.alpha :as s]
|
||||
#?(:clj [orchestra.core :refer [defn-spec]]
|
||||
:cljs [orchestra.core :refer-macros [defn-spec]])
|
||||
[dda.c4k-common.common :as cm]
|
||||
[dda.c4k-common.predicate :as cp]
|
||||
[dda.c4k-common.monitoring :as mon]
|
||||
[dda.c4k-common.yaml :as yaml]
|
||||
[dda.c4k-jitsi.jitsi :as jitsi]))
|
||||
|
||||
(def config-defaults {:issuer :staging})
|
||||
(def config-defaults {:issuer "staging"})
|
||||
|
||||
(s/def ::mon-cfg mon/config?)
|
||||
(s/def ::mon-auth mon/auth?)
|
||||
|
||||
(def config? (s/keys :req-un [::jitsi/fqdn]
|
||||
:opt-un [::jitsi/issuer ::jitsi/ingress-type]))
|
||||
:opt-un [::jitsi/issuer
|
||||
::mon-cfg]))
|
||||
|
||||
(def auth? (s/keys :req-un [::jitsi/jvb-auth-password ::jitsi/jicofo-auth-password ::jitsi/jicofo-component-secret]))
|
||||
(def auth? (s/keys :req-un [::jitsi/jvb-auth-password
|
||||
::jitsi/jicofo-auth-password
|
||||
::jitsi/jicofo-component-secret]
|
||||
:opt-un [::mon-auth]))
|
||||
|
||||
(defn k8s-objects [config]
|
||||
(defn-spec k8s-objects cp/map-or-seq?
|
||||
[config config?
|
||||
auth auth?]
|
||||
(map yaml/to-string
|
||||
[(jitsi/generate-secret-jitsi config)
|
||||
(jitsi/generate-certificate-jitsi config)
|
||||
(jitsi/generate-certificate-etherpad config)
|
||||
(jitsi/generate-jvb-service)
|
||||
(jitsi/generate-web-service)
|
||||
(jitsi/generate-etherpad-service)
|
||||
(jitsi/generate-ingress-jitsi config)
|
||||
(jitsi/generate-ingress-etherpad config)
|
||||
(jitsi/generate-deployment config)]))
|
||||
|
||||
(defn-spec generate any?
|
||||
[my-config config?
|
||||
my-auth auth?]
|
||||
(let [resulting-config (merge config-defaults my-config my-auth)]
|
||||
(cs/join
|
||||
"\n---\n"
|
||||
(k8s-objects resulting-config))))
|
||||
(filter
|
||||
#(not (nil? %))
|
||||
(cm/concat-vec
|
||||
[(jitsi/generate-secret-jitsi auth)
|
||||
(jitsi/generate-jvb-service)
|
||||
(jitsi/generate-web-service)
|
||||
(jitsi/generate-etherpad-service)
|
||||
(jitsi/generate-deployment config)]
|
||||
(jitsi/generate-ingress-web config)
|
||||
(jitsi/generate-ingress-etherpad config)
|
||||
(when (:contains? config :mon-cfg)
|
||||
(mon/generate (:mon-cfg config) (:mon-auth auth)))))))
|
||||
|
|
|
|||
|
|
@ -2,95 +2,78 @@
|
|||
(:require
|
||||
[clojure.spec.alpha :as s]
|
||||
#?(:cljs [shadow.resource :as rc])
|
||||
#?(:clj [orchestra.core :refer [defn-spec]]
|
||||
:cljs [orchestra.core :refer-macros [defn-spec]])
|
||||
[dda.c4k-common.yaml :as yaml]
|
||||
[dda.c4k-common.common :as cm]
|
||||
[dda.c4k-common.ingress :as ing]
|
||||
[dda.c4k-common.base64 :as b64]
|
||||
[dda.c4k-common.predicate :as pred]))
|
||||
[dda.c4k-common.predicate :as cp]))
|
||||
|
||||
(s/def ::fqdn pred/fqdn-string?)
|
||||
(s/def ::issuer pred/letsencrypt-issuer?)
|
||||
(s/def ::jvb-auth-password pred/bash-env-string?)
|
||||
(s/def ::jicofo-auth-password pred/bash-env-string?)
|
||||
(s/def ::jicofo-component-secret pred/bash-env-string?)
|
||||
(s/def ::fqdn cp/fqdn-string?)
|
||||
(s/def ::issuer cp/letsencrypt-issuer?)
|
||||
(s/def ::jvb-auth-password cp/bash-env-string?)
|
||||
(s/def ::jicofo-auth-password cp/bash-env-string?)
|
||||
(s/def ::jicofo-component-secret cp/bash-env-string?)
|
||||
|
||||
(def config? (s/keys :req-un [::fqdn]
|
||||
:opt-un [::issuer]))
|
||||
|
||||
(def auth? (s/keys :req-un [::jvb-auth-password
|
||||
::jicofo-auth-password
|
||||
::jicofo-component-secret]))
|
||||
|
||||
#?(:cljs
|
||||
(defmethod yaml/load-resource :jitsi [resource-name]
|
||||
(case resource-name
|
||||
"jitsi/deployment.yaml" (rc/inline "jitsi/deployment.yaml")
|
||||
"jitsi/etherpad-service.yaml" (rc/inline "jitsi/etherpad-service.yaml")
|
||||
"jitsi/ingress-jitsi.yaml" (rc/inline "jitsi/ingress-jitsi.yaml")
|
||||
"jitsi/ingress-etherpad.yaml" (rc/inline "jitsi/ingress-etherpad.yaml")
|
||||
"jitsi/jvb-service.yaml" (rc/inline "jitsi/jvb-service.yaml")
|
||||
"jitsi/secret.yaml" (rc/inline "jitsi/secret.yaml")
|
||||
"jitsi/web-service.yaml" (rc/inline "jitsi/web-service.yaml")
|
||||
(throw (js/Error. "Undefined Resource!")))))
|
||||
|
||||
(defn generate-ingress-jitsi [config]
|
||||
(let [{:keys [fqdn issuer ingress-type]
|
||||
:or {issuer :staging ingress-type :default}} config
|
||||
letsencrypt-issuer (name issuer)
|
||||
ingress-kind (if (= :default ingress-type) "" (name ingress-type))]
|
||||
(->
|
||||
(yaml/from-string (yaml/load-resource "jitsi/ingress-jitsi.yaml"))
|
||||
(assoc-in [:metadata :annotations :cert-manager.io/cluster-issuer] letsencrypt-issuer)
|
||||
(assoc-in [:metadata :annotations :kubernetes.io/ingress.class] ingress-kind)
|
||||
(cm/replace-all-matching-values-by-new-value "REPLACE_JITSI_FQDN" fqdn))))
|
||||
(defn-spec generate-ingress-web cp/map-or-seq?
|
||||
[config config?]
|
||||
(ing/generate-ingress-and-cert
|
||||
(merge
|
||||
{:service-name "web"
|
||||
:service-port 80
|
||||
:fqdns [(:fqdn config)]}
|
||||
config)))
|
||||
|
||||
(defn generate-ingress-etherpad [config]
|
||||
(let [{:keys [fqdn issuer ingress-type]
|
||||
:or {issuer :staging ingress-type :default}} config
|
||||
letsencrypt-issuer (name issuer)
|
||||
ingress-kind (if (= :default ingress-type) "" (name ingress-type))]
|
||||
(->
|
||||
(yaml/from-string (yaml/load-resource "jitsi/ingress-etherpad.yaml"))
|
||||
(assoc-in [:metadata :annotations :cert-manager.io/cluster-issuer] letsencrypt-issuer)
|
||||
(assoc-in [:metadata :annotations :kubernetes.io/ingress.class] ingress-kind)
|
||||
(cm/replace-all-matching-values-by-new-value "REPLACE_ETHERPAD_FQDN"
|
||||
(str "etherpad." fqdn)))))
|
||||
(defn-spec generate-ingress-etherpad cp/map-or-seq?
|
||||
[config config?]
|
||||
(ing/generate-ingress-and-cert
|
||||
(merge
|
||||
{:service-name "etherpad"
|
||||
:service-port 9001
|
||||
:fqdns [(str "etherpad." (:fqdn config))]}
|
||||
config)))
|
||||
|
||||
(defn generate-secret-jitsi [config]
|
||||
(let [{:keys [jvb-auth-password jicofo-auth-password jicofo-component-secret]} config]
|
||||
(defn-spec generate-secret-jitsi cp/map-or-seq?
|
||||
[auth auth?]
|
||||
(let [{:keys [jvb-auth-password jicofo-auth-password jicofo-component-secret]} auth]
|
||||
(->
|
||||
(yaml/from-string (yaml/load-resource "jitsi/secret.yaml"))
|
||||
(cm/replace-key-value :JVB_AUTH_PASSWORD (b64/encode jvb-auth-password))
|
||||
(cm/replace-key-value :JICOFO_AUTH_PASSWORD (b64/encode jicofo-auth-password))
|
||||
(cm/replace-key-value :JICOFO_COMPONENT_SECRET (b64/encode jicofo-component-secret)))))
|
||||
|
||||
(defn generate-jvb-service []
|
||||
(defn-spec generate-jvb-service cp/map-or-seq? []
|
||||
(yaml/from-string (yaml/load-resource "jitsi/jvb-service.yaml")))
|
||||
|
||||
(defn generate-web-service []
|
||||
(yaml/from-string (yaml/load-resource "jitsi/web-service.yaml")))
|
||||
(defn-spec generate-web-service cp/map-or-seq? []
|
||||
(yaml/load-as-edn "jitsi/web-service.yaml"))
|
||||
|
||||
(defn generate-etherpad-service []
|
||||
(yaml/from-string (yaml/load-resource "jitsi/etherpad-service.yaml")))
|
||||
(defn-spec generate-etherpad-service cp/map-or-seq? []
|
||||
(yaml/load-as-edn "jitsi/etherpad-service.yaml"))
|
||||
|
||||
(defn generate-deployment [config]
|
||||
(defn-spec generate-deployment cp/map-or-seq?
|
||||
[config config?]
|
||||
(let [{:keys [fqdn]} config]
|
||||
(->
|
||||
(yaml/from-string (yaml/load-resource "jitsi/deployment.yaml"))
|
||||
(yaml/load-as-edn "jitsi/deployment.yaml")
|
||||
(cm/replace-all-matching-values-by-new-value "REPLACE_JITSI_FQDN" fqdn)
|
||||
(cm/replace-all-matching-values-by-new-value "REPLACE_ETHERPAD_URL"
|
||||
(str "https://etherpad." fqdn "/p/")))))
|
||||
|
||||
(defn generate-certificate-jitsi
|
||||
[config]
|
||||
(let [{:keys [fqdn issuer ingress-type]
|
||||
:or {issuer :staging ingress-type :default}} config
|
||||
letsencrypt-issuer (name issuer)
|
||||
ingress-kind (if (= :default ingress-type) "" (name ingress-type))]
|
||||
(->
|
||||
(yaml/load-as-edn "jitsi/certificate-jitsi.yaml")
|
||||
(assoc-in [:spec :issuerRef :name] letsencrypt-issuer)
|
||||
(cm/replace-all-matching-values-by-new-value "REPLACE_JITSI_FQDN" fqdn))))
|
||||
|
||||
(defn generate-certificate-etherpad
|
||||
[config]
|
||||
(let [{:keys [fqdn issuer ingress-type]
|
||||
:or {issuer :staging ingress-type :default}} config
|
||||
letsencrypt-issuer (name issuer)
|
||||
ingress-kind (if (= :default ingress-type) "" (name ingress-type))]
|
||||
(->
|
||||
(yaml/load-as-edn "jitsi/certificate-etherpad.yaml")
|
||||
(assoc-in [:spec :issuerRef :name] letsencrypt-issuer)
|
||||
(cm/replace-all-matching-values-by-new-value "REPLACE_ETHERPAD_FQDN" (str "etherpad." fqdn)))))
|
||||
|
|
@ -1,24 +1,37 @@
|
|||
(ns dda.c4k-jitsi.browser
|
||||
(:require
|
||||
[clojure.tools.reader.edn :as edn]
|
||||
[dda.c4k-jitsi.core :as core]
|
||||
[dda.c4k-jitsi.jitsi :as jitsi]
|
||||
[dda.c4k-common.monitoring :as mon]
|
||||
[dda.c4k-common.common :as cm]
|
||||
[dda.c4k-common.browser :as br]
|
||||
[dda.c4k-common.postgres :as pgc]))
|
||||
[dda.c4k-jitsi.core :as core]
|
||||
[dda.c4k-jitsi.jitsi :as jitsi]))
|
||||
|
||||
(defn generate-content
|
||||
[]
|
||||
(into [] (concat [(assoc (br/generate-needs-validation) :content
|
||||
(into [] (concat (br/generate-input-field "fqdn" "Your fqdn:" "jitsi.prod.meissa-gmbh.de")
|
||||
(br/generate-input-field "issuer" "(Optional) Your issuer prod/staging:" "")
|
||||
[(br/generate-br)]
|
||||
(br/generate-text-area "auth" "Your auth.edn:" "{:jvb-auth-password \"jitsi\"
|
||||
:jicofo-auth-password \"jicofo-password\"
|
||||
:jicofo-component-secret \"jicofo-component-secrect\"}"
|
||||
"5")
|
||||
[(br/generate-br)]
|
||||
(br/generate-button "generate-button" "Generate c4k yaml"))))]
|
||||
(br/generate-output "c4k-jitsi-output" "Your c4k deployment.yaml:" "25"))))
|
||||
(defn generate-content []
|
||||
(cm/concat-vec
|
||||
[(assoc
|
||||
(br/generate-needs-validation) :content
|
||||
(cm/concat-vec
|
||||
(br/generate-group
|
||||
"domain"
|
||||
(cm/concat-vec
|
||||
(br/generate-input-field "fqdn" "Your fqdn:" "jitsi.prod.meissa-gmbh.de")
|
||||
(br/generate-input-field "issuer" "(Optional) Your issuer prod/staging:" "")
|
||||
(br/generate-input-field "mon-cluster-name" "(Optional) monitoring cluster name:" "jitsi")
|
||||
(br/generate-input-field "mon-cluster-stage" "(Optional) monitoring cluster stage:" "test")
|
||||
(br/generate-input-field "mon-cloud-url" "(Optional) grafana cloud url:" "https://prometheus-prod-01-eu-west-0.grafana.net/api/prom/push")
|
||||
))
|
||||
(br/generate-group
|
||||
"credentials"
|
||||
(br/generate-text-area "auth" "Your auth.edn:" "{:jvb-auth-password \"jitsi\"
|
||||
:jicofo-auth-password \"jicofo-password\"
|
||||
:jicofo-component-secret \"jicofo-component-secrect\"
|
||||
:mon-auth {:grafana-cloud-user \"your-user-id\"
|
||||
:grafana-cloud-password \"your-cloud-password\"}}}"
|
||||
"5"))
|
||||
[(br/generate-br)]
|
||||
(br/generate-button "generate-button" "Generate c4k yaml")))]
|
||||
(br/generate-output "c4k-jitsi-output" "Your c4k deployment.yaml:" "25")))
|
||||
|
||||
(defn generate-content-div
|
||||
[]
|
||||
|
|
@ -28,16 +41,26 @@
|
|||
(generate-content)})
|
||||
|
||||
(defn config-from-document []
|
||||
(let [issuer (br/get-content-from-element "issuer" :optional true :deserializer keyword)]
|
||||
(let [issuer (br/get-content-from-element "issuer" :optional true)
|
||||
mon-cluster-name (br/get-content-from-element "mon-cluster-name" :optional true)
|
||||
mon-cluster-stage (br/get-content-from-element "mon-cluster-stage" :optional true :deserializer keyword)
|
||||
mon-cloud-url (br/get-content-from-element "mon-cloud-url" :optional true)]
|
||||
(merge
|
||||
{:fqdn (br/get-content-from-element "fqdn")}
|
||||
(when (some? issuer)
|
||||
{:issuer issuer})
|
||||
(when (some? mon-cluster-name)
|
||||
{:mon-cfg {:cluster-name mon-cluster-name
|
||||
:cluster-stage (keyword mon-cluster-stage)
|
||||
:grafana-cloud-url mon-cloud-url}})
|
||||
)))
|
||||
|
||||
(defn validate-all! []
|
||||
(br/validate! "fqdn" ::jitsi/fqdn)
|
||||
(br/validate! "issuer" ::jitsi/issuer :optional true :deserializer keyword)
|
||||
(br/validate! "issuer" ::jitsi/issuer :optional true)
|
||||
(br/validate! "mon-cluster-name" ::mon/cluster-name :optional true)
|
||||
(br/validate! "mon-cluster-stage" ::mon/cluster-stage :optional true :deserializer keyword)
|
||||
(br/validate! "mon-cloud-url" ::mon/grafana-cloud-url :optional true)
|
||||
(br/validate! "auth" core/auth? :deserializer edn/read-string)
|
||||
(br/set-validated!))
|
||||
|
||||
|
|
@ -52,10 +75,15 @@
|
|||
(.getElementById "generate-button")
|
||||
(.addEventListener "click"
|
||||
#(do (validate-all!)
|
||||
(-> (core/generate
|
||||
(-> (cm/generate-common
|
||||
(config-from-document)
|
||||
(br/get-content-from-element "auth" :deserializer edn/read-string))
|
||||
(br/get-content-from-element "auth" :deserializer edn/read-string)
|
||||
{}
|
||||
core/k8s-objects)
|
||||
(br/set-output!)))))
|
||||
(add-validate-listener "fqdn")
|
||||
(add-validate-listener "fqdn")
|
||||
(add-validate-listener "issuer")
|
||||
(add-validate-listener "mon-cluster-name")
|
||||
(add-validate-listener "mon-cluster-stage")
|
||||
(add-validate-listener "mon-cloud-url")
|
||||
(add-validate-listener "auth"))
|
||||
|
|
@ -1,15 +0,0 @@
|
|||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: etherpad-cert
|
||||
namespace: default
|
||||
spec:
|
||||
secretName: etherpad-cert
|
||||
commonName: REPLACE_ETHERPAD_FQDN
|
||||
duration: 2160h # 90d
|
||||
renewBefore: 360h # 15d
|
||||
dnsNames:
|
||||
- REPLACE_ETHERPAD_FQDN
|
||||
issuerRef:
|
||||
name: REPLACEME
|
||||
kind: ClusterIssuer
|
||||
|
|
@ -1,15 +0,0 @@
|
|||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: jitsi-cert
|
||||
namespace: default
|
||||
spec:
|
||||
secretName: jitsi-cert
|
||||
commonName: REPLACE_JITSI_FQDN
|
||||
duration: 2160h # 90d
|
||||
renewBefore: 360h # 15d
|
||||
dnsNames:
|
||||
- REPLACE_JITSI_FQDN
|
||||
issuerRef:
|
||||
name: REPLACEME
|
||||
kind: ClusterIssuer
|
||||
|
|
@ -1,23 +0,0 @@
|
|||
apiVersion: networking.k8s.io/v1
|
||||
kind: Ingress
|
||||
metadata:
|
||||
name: etherpad
|
||||
annotations:
|
||||
cert-manager.io/cluster-issuer: REPLACEME
|
||||
ingress.kubernetes.io/ssl-redirect: "true"
|
||||
spec:
|
||||
tls:
|
||||
- hosts:
|
||||
- REPLACE_ETHERPAD_FQDN
|
||||
secretName: etherpad-cert
|
||||
rules:
|
||||
- host: REPLACE_ETHERPAD_FQDN
|
||||
http:
|
||||
paths:
|
||||
- path: /
|
||||
pathType: Prefix
|
||||
backend:
|
||||
service:
|
||||
name: etherpad
|
||||
port:
|
||||
number: 9001
|
||||
|
|
@ -1,23 +0,0 @@
|
|||
apiVersion: networking.k8s.io/v1
|
||||
kind: Ingress
|
||||
metadata:
|
||||
name: jitsi
|
||||
annotations:
|
||||
cert-manager.io/cluster-issuer: REPLACEME
|
||||
ingress.kubernetes.io/ssl-redirect: "true"
|
||||
spec:
|
||||
tls:
|
||||
- hosts:
|
||||
- REPLACE_JITSI_FQDN
|
||||
secretName: jitsi-cert
|
||||
rules:
|
||||
- host: REPLACE_JITSI_FQDN
|
||||
http:
|
||||
paths:
|
||||
- path: /
|
||||
pathType: Prefix
|
||||
backend:
|
||||
service:
|
||||
name: web
|
||||
port:
|
||||
number: 80
|
||||
20
src/test/cljc/dda/c4k_jitsi/core_test.cljc
Normal file
20
src/test/cljc/dda/c4k_jitsi/core_test.cljc
Normal file
|
|
@ -0,0 +1,20 @@
|
|||
(ns dda.c4k-jitsi.core-test
|
||||
(:require
|
||||
#?(:cljs [shadow.resource :as rc])
|
||||
#?(:clj [clojure.test :refer [deftest is are testing run-tests]]
|
||||
:cljs [cljs.test :refer-macros [deftest is are testing run-tests]])
|
||||
[clojure.spec.alpha :as s]
|
||||
[dda.c4k-common.yaml :as yaml]
|
||||
[dda.c4k-jitsi.core :as cut]))
|
||||
|
||||
#?(:cljs
|
||||
(defmethod yaml/load-resource :jitsi-test [resource-name]
|
||||
(case resource-name
|
||||
"jitsi-test/valid-auth.yaml" (rc/inline "jitsi-test/valid-auth.yaml")
|
||||
"jitsi-test/valid-config.yaml" (rc/inline "jitsi-test/valid-config.yaml")
|
||||
(throw (js/Error. "Undefined Resource!")))))
|
||||
|
||||
(deftest validate-valid-resources
|
||||
(is (s/valid? cut/config? (yaml/load-as-edn "jitsi-test/valid-config.yaml")))
|
||||
(is (s/valid? cut/auth? (yaml/load-as-edn "jitsi-test/valid-auth.yaml")))
|
||||
)
|
||||
|
|
@ -5,7 +5,7 @@
|
|||
[clojure.spec.test.alpha :as st]
|
||||
[dda.c4k-jitsi.jitsi :as cut]))
|
||||
|
||||
;;(st/instrument)
|
||||
(st/instrument)
|
||||
|
||||
(deftest should-generate-deployment
|
||||
(is (= {:apiVersion "apps/v1",
|
||||
|
|
@ -37,7 +37,7 @@
|
|||
:image "jitsi/prosody:stable-7287",
|
||||
:imagePullPolicy "IfNotPresent",
|
||||
:env
|
||||
[{:name "PUBLIC_URL", :value "xy"}
|
||||
[{:name "PUBLIC_URL", :value "xy.xy.xy"}
|
||||
{:name "XMPP_DOMAIN", :value "meet.meissa-gmbh"}
|
||||
{:name "XMPP_AUTH_DOMAIN", :value "auth.meet.meissa-gmbh"}
|
||||
{:name "XMPP_MUC_DOMAIN", :value "muc.meet.meissa-gmbh"}
|
||||
|
|
@ -54,7 +54,7 @@
|
|||
:image "domaindrivenarchitecture/c4k-jitsi",
|
||||
:imagePullPolicy "IfNotPresent",
|
||||
:env
|
||||
[{:name "PUBLIC_URL", :value "xy"}
|
||||
[{:name "PUBLIC_URL", :value "xy.xy.xy"}
|
||||
{:name "XMPP_SERVER", :value "localhost"}
|
||||
{:name "JICOFO_AUTH_USER", :value "focus"}
|
||||
{:name "XMPP_DOMAIN", :value "meet.meissa-gmbh"}
|
||||
|
|
@ -70,14 +70,14 @@
|
|||
{:name "RESOLUTION_WIDTH", :value "853"}
|
||||
{:name "RESOLUTION_WIDTH_MIN", :value "427"}
|
||||
{:name "DISABLE_AUDIO_LEVELS", :value "true"}
|
||||
{:name "ETHERPAD_PUBLIC_URL", :value "https://etherpad.xy/p/"}]}
|
||||
{:name "ETHERPAD_PUBLIC_URL", :value "https://etherpad.xy.xy.xy/p/"}]}
|
||||
{:name "jvb",
|
||||
:image "jitsi/jvb:stable-7287",
|
||||
:imagePullPolicy "IfNotPresent",
|
||||
:env
|
||||
[{:name "PUBLIC_URL", :value "xy"}
|
||||
[{:name "PUBLIC_URL", :value "xy.xy.xy"}
|
||||
{:name "XMPP_SERVER", :value "localhost"}
|
||||
{:name "DOCKER_HOST_ADDRESS", :value "xy"}
|
||||
{:name "DOCKER_HOST_ADDRESS", :value "xy.xy.xy"}
|
||||
{:name "XMPP_DOMAIN", :value "meet.meissa-gmbh"}
|
||||
{:name "XMPP_AUTH_DOMAIN", :value "auth.meet.meissa-gmbh"}
|
||||
{:name "XMPP_INTERNAL_MUC_DOMAIN", :value "internal-muc.meet.meissa-gmbh"}
|
||||
|
|
@ -102,45 +102,7 @@
|
|||
{:name "XMPP_INTERNAL_MUC_DOMAIN", :value "internal-muc.meet.meissa-gmbh"}
|
||||
{:name "JICOFO_AUTH_PASSWORD", :valueFrom {:secretKeyRef {:name "jitsi-config", :key "JICOFO_AUTH_PASSWORD"}}}
|
||||
{:name "TZ", :value "Europe/Berlin"}]}]}}}}
|
||||
(cut/generate-deployment {:fqdn "xy"}))))
|
||||
|
||||
(deftest should-generate-ingress-jitsi
|
||||
(is (= {:apiVersion "networking.k8s.io/v1",
|
||||
:kind "Ingress",
|
||||
:metadata
|
||||
{:name "jitsi",
|
||||
:annotations
|
||||
{:cert-manager.io/cluster-issuer "staging",
|
||||
:ingress.kubernetes.io/ssl-redirect "true",
|
||||
:kubernetes.io/ingress.class ""}},
|
||||
:spec
|
||||
{:tls [{:hosts ["test.com"], :secretName "jitsi-cert"}],
|
||||
:rules
|
||||
[{:host "test.com",
|
||||
:http {:paths [{:path "/", :pathType "Prefix", :backend {:service {:name "web", :port {:number 80}}}}]}}]}}
|
||||
(cut/generate-ingress-jitsi {:fqdn "test.com" :issuer :staging}))))
|
||||
|
||||
(deftest should-generate-ingress-etherpad
|
||||
(is (= {:apiVersion "networking.k8s.io/v1",
|
||||
:kind "Ingress",
|
||||
:metadata
|
||||
{:name "etherpad",
|
||||
:annotations
|
||||
{:cert-manager.io/cluster-issuer "staging",
|
||||
:ingress.kubernetes.io/ssl-redirect "true",
|
||||
:kubernetes.io/ingress.class ""}},
|
||||
:spec
|
||||
{:tls [{:hosts ["etherpad.test.com"], :secretName "etherpad-cert"}],
|
||||
:rules
|
||||
[{:host "etherpad.test.com",
|
||||
:http
|
||||
{:paths
|
||||
[{:path "/",
|
||||
:pathType "Prefix",
|
||||
:backend
|
||||
{:service {:name "etherpad", :port {:number 9001}}}}]}}]}}
|
||||
(cut/generate-ingress-etherpad {:fqdn "test.com" :issuer :staging}))))
|
||||
|
||||
(cut/generate-deployment {:fqdn "xy.xy.xy"}))))
|
||||
|
||||
(deftest should-generate-secret
|
||||
(is (= {:apiVersion "v1",
|
||||
|
|
|
|||
6
src/test/resources/jitsi-test/valid-auth.yaml
Normal file
6
src/test/resources/jitsi-test/valid-auth.yaml
Normal file
|
|
@ -0,0 +1,6 @@
|
|||
jvb-auth-password: "JvbAuth"
|
||||
jicofo-auth-password: "JicofoAuth"
|
||||
jicofo-component-secret: "JicofoCompSec"
|
||||
mon-auth:
|
||||
grafana-cloud-user: "user"
|
||||
grafana-cloud-password: "password"
|
||||
6
src/test/resources/jitsi-test/valid-config.yaml
Normal file
6
src/test/resources/jitsi-test/valid-config.yaml
Normal file
|
|
@ -0,0 +1,6 @@
|
|||
fqdn: "jitsi.test.meissa-gmbh.de"
|
||||
issuer: "staging"
|
||||
mon-cfg:
|
||||
grafana-cloud-url: "url-for-your-prom-remote-write-endpoint"
|
||||
cluster-name: "jitsi"
|
||||
cluster-stage: "test"
|
||||
216
test.yaml
216
test.yaml
|
|
@ -1,216 +0,0 @@
|
|||
kind: Ingress
|
||||
apiVersion: networking.k8s.io/v1
|
||||
metadata:
|
||||
name: jitsi
|
||||
annotations:
|
||||
cert-manager.io/cluster-issuer: letsencrypt-staging-issuer
|
||||
kubernetes.io/ingress.class: ''
|
||||
spec:
|
||||
tls:
|
||||
- hosts:
|
||||
- jitsi.test.meissa-gmbh.de
|
||||
secretName: tls-jitsi
|
||||
rules:
|
||||
- host: jitsi.test.meissa-gmbh.de
|
||||
http:
|
||||
paths:
|
||||
- path: /
|
||||
pathType: Prefix
|
||||
backend:
|
||||
service:
|
||||
name: web
|
||||
port:
|
||||
number: 80
|
||||
|
||||
---
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: jitsi-config
|
||||
type: Opaque
|
||||
data:
|
||||
JVB_AUTH_PASSWORD: SnZiQXV0aA==
|
||||
JICOFO_AUTH_PASSWORD: Smljb2ZvQXV0aA==
|
||||
JICOFO_COMPONENT_SECRET: Smljb2ZvQ29tcFNlYw==
|
||||
|
||||
---
|
||||
- apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
labels:
|
||||
service: jvb
|
||||
name: jvb-udp
|
||||
spec:
|
||||
type: NodePort
|
||||
externalTrafficPolicy: Cluster
|
||||
ports:
|
||||
- port: 30300
|
||||
protocol: UDP
|
||||
targetPort: 30300
|
||||
nodePort: 30300
|
||||
selector:
|
||||
app: jitsi
|
||||
- apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
labels:
|
||||
service: web
|
||||
name: web
|
||||
spec:
|
||||
ports:
|
||||
- name: http
|
||||
port: 80
|
||||
targetPort: 80
|
||||
- name: https
|
||||
port: 443
|
||||
targetPort: 443
|
||||
selector:
|
||||
app: jitsi
|
||||
- apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
labels:
|
||||
app: jitsi
|
||||
name: jitsi
|
||||
spec:
|
||||
strategy:
|
||||
type: Recreate
|
||||
selector:
|
||||
matchLabels:
|
||||
app: jitsi
|
||||
template:
|
||||
metadata:
|
||||
labels:
|
||||
app: jitsi
|
||||
spec:
|
||||
containers:
|
||||
- name: jicofo
|
||||
image: jitsi/jicofo:stable-6826
|
||||
imagePullPolicy: IfNotPresent
|
||||
env:
|
||||
- name: XMPP_SERVER
|
||||
value: localhost
|
||||
- name: XMPP_DOMAIN
|
||||
value: meet.jitsi
|
||||
- name: XMPP_AUTH_DOMAIN
|
||||
value: auth.meet.jitsi
|
||||
- name: XMPP_MUC_DOMAIN
|
||||
value: muc.meet.jitsi
|
||||
- name: XMPP_INTERNAL_MUC_DOMAIN
|
||||
value: internal-muc.meet.jitsi
|
||||
- name: JICOFO_COMPONENT_SECRET
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: jitsi-config
|
||||
key: JICOFO_COMPONENT_SECRET
|
||||
- name: JICOFO_AUTH_USER
|
||||
value: focus
|
||||
- name: JICOFO_AUTH_PASSWORD
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: jitsi-config
|
||||
key: JICOFO_AUTH_PASSWORD
|
||||
- name: TZ
|
||||
value: Europe/Berlin
|
||||
- name: JVB_BREWERY_MUC
|
||||
value: jvbbrewery
|
||||
- name: prosody
|
||||
image: jitsi/prosody:stable-6826
|
||||
imagePullPolicy: IfNotPresent
|
||||
env:
|
||||
- name: PUBLIC_URL
|
||||
value: https://jitsi.test.meissa-gmbh.de
|
||||
- name: XMPP_DOMAIN
|
||||
value: meet.jitsi
|
||||
- name: XMPP_AUTH_DOMAIN
|
||||
value: auth.meet.jitsi
|
||||
- name: XMPP_MUC_DOMAIN
|
||||
value: muc.meet.jitsi
|
||||
- name: XMPP_INTERNAL_MUC_DOMAIN
|
||||
value: internal-muc.meet.jitsi
|
||||
- name: JICOFO_COMPONENT_SECRET
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: jitsi-config
|
||||
key: JICOFO_COMPONENT_SECRET
|
||||
- name: JVB_AUTH_USER
|
||||
value: jvb
|
||||
- name: JVB_AUTH_PASSWORD
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: jitsi-config
|
||||
key: JVB_AUTH_PASSWORD
|
||||
- name: JICOFO_AUTH_USER
|
||||
value: focus
|
||||
- name: JICOFO_AUTH_PASSWORD
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: jitsi-config
|
||||
key: JICOFO_AUTH_PASSWORD
|
||||
- name: TZ
|
||||
value: Europe/Berlin
|
||||
- name: JVB_TCP_HARVESTER_DISABLED
|
||||
value: 'true'
|
||||
- name: web
|
||||
image: jitsi/web:stable-6826
|
||||
imagePullPolicy: IfNotPresent
|
||||
env:
|
||||
- name: PUBLIC_URL
|
||||
value: https://jitsi.test.meissa-gmbh.de
|
||||
- name: XMPP_SERVER
|
||||
value: localhost
|
||||
- name: JICOFO_AUTH_USER
|
||||
value: focus
|
||||
- name: XMPP_DOMAIN
|
||||
value: meet.jitsi
|
||||
- name: XMPP_AUTH_DOMAIN
|
||||
value: auth.meet.jitsi
|
||||
- name: XMPP_INTERNAL_MUC_DOMAIN
|
||||
value: internal-muc.meet.jitsi
|
||||
- name: XMPP_BOSH_URL_BASE
|
||||
value: http://127.0.0.1:5280
|
||||
- name: XMPP_MUC_DOMAIN
|
||||
value: muc.meet.jitsi
|
||||
- name: TZ
|
||||
value: Europe/Berlin
|
||||
- name: JVB_TCP_HARVESTER_DISABLED
|
||||
value: 'true'
|
||||
- name: jvb
|
||||
image: jitsi/jvb:stable-6826
|
||||
imagePullPolicy: IfNotPresent
|
||||
env:
|
||||
- name: XMPP_SERVER
|
||||
value: localhost
|
||||
- name: DOCKER_HOST_ADDRESS
|
||||
value: localhost
|
||||
- name: XMPP_DOMAIN
|
||||
value: meet.jitsi
|
||||
- name: XMPP_AUTH_DOMAIN
|
||||
value: auth.meet.jitsi
|
||||
- name: XMPP_INTERNAL_MUC_DOMAIN
|
||||
value: internal-muc.meet.jitsi
|
||||
- name: JVB_STUN_SERVERS
|
||||
value: stun.1und1.de:3478,stun.t-online.de:3478,stun.hosteurope.de:3478
|
||||
- name: JICOFO_AUTH_USER
|
||||
value: focus
|
||||
- name: JVB_TCP_HARVESTER_DISABLED
|
||||
value: 'true'
|
||||
- name: JVB_AUTH_USER
|
||||
value: jvb
|
||||
- name: JVB_PORT
|
||||
value: '30300'
|
||||
- name: JVB_AUTH_PASSWORD
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: jitsi-config
|
||||
key: JVB_AUTH_PASSWORD
|
||||
- name: JICOFO_AUTH_PASSWORD
|
||||
valueFrom:
|
||||
secretKeyRef:
|
||||
name: jitsi-config
|
||||
key: JICOFO_AUTH_PASSWORD
|
||||
- name: JVB_BREWERY_MUC
|
||||
value: jvbbrewery
|
||||
- name: TZ
|
||||
value: Europe/Berlin
|
||||
|
||||
|
|
@ -1,3 +0,0 @@
|
|||
{:jvb-auth-password "JvbAuth"
|
||||
:jicofo-auth-password "JicofoAuth"
|
||||
:jicofo-component-secret "JicofoCompSec"}
|
||||
|
|
@ -1,2 +0,0 @@
|
|||
{:fqdn "jitsi.test.meissa-gmbh.de"
|
||||
:issuer :staging}
|
||||
Loading…
Add table
Reference in a new issue